National Clean Out Your Computer Day

According to the National Day Calendar, every second Monday in February is supposed to be a day to take some time out of your busy schedule to care for your computer. Over time your computer gets clogged up and like anything, needs a good clean out and organise! Heres a few tips to get you started:
Save your important files properly
We all do it, quickly save a file that we’re working on to our desktop to find it quickly for when we next need to access it. However, this is a dangerous game. If your computer suddenly goes pop one day, this won’t be backed up and it’ll take you a lot more time and effort to recreate the file, than just saving it to your company’s drive on the server. Today, make sure you’ve saved anything you don’t want to lose, to your company drive.
Stop postponing that Windows Update
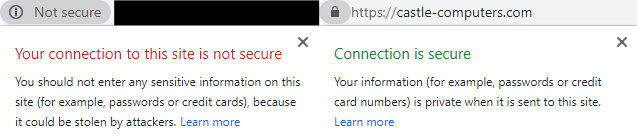
If you want your computer to be organised and up to date – its best to get your Windows Updates done. Why? Lots of programs you use need to be updated because of security. If you’re not on the latest version of a program/software, your information is not fully secure. If you’ve been postponing a Windows Update, why don’t you schedule it for when you’re leaving work today so that it doesn’t interrupt your work. Get in touch with any queries about your Windows Updates.
Sort out your emails
Delete old emails that you don’t have a valid reason for keeping (keeps you GDPR compliant too!) If you use Outlook, set up Rules to help deal with the constant flow of emails. This organises your emails automatically and makes it more obvious to see urgent emails that you need to action. For advice on setting up Rules, contact us.
For more advice and handy tips on getting organised on your computer, read our blog post at http://bit.ly/2RSEp0a. Contact us if you need any advice!




 If you have an Office 365 account, it’s highly recommended to set up two-step verification/multi-factor authentication. It adds an extra layer of security to your Office 365 account. You sign in with your password as well as a verification code that is sent to you by text message. This will protect your account by making it a lot more difficult for someone else to sign in. Contact us for help on setting this up!
If you have an Office 365 account, it’s highly recommended to set up two-step verification/multi-factor authentication. It adds an extra layer of security to your Office 365 account. You sign in with your password as well as a verification code that is sent to you by text message. This will protect your account by making it a lot more difficult for someone else to sign in. Contact us for help on setting this up! Nowadays, where there are more security threats than ever before – having any old Anti-Virus is just not good enough. You need the best protection out there for your business. You might have anti-virus installed – but is it working? Thankfully, we know a few things about anti-virus and can check if it’s working and if you do need to install some – recommend the best software out there.
Nowadays, where there are more security threats than ever before – having any old Anti-Virus is just not good enough. You need the best protection out there for your business. You might have anti-virus installed – but is it working? Thankfully, we know a few things about anti-virus and can check if it’s working and if you do need to install some – recommend the best software out there.

 Ahhhh passwords! Seemingly the simplest way of protecting your secure information but somehow the one that so many fail on. Passwords should be strong, complex & memorable to only you. That means including numbers, punctuations, capital letters etc. They shouldn’t be obvious words like the same as your username, the word ‘password’ or your husband’s name (hackers have facebook too!) You should change your password at times too (eg every couple of months). We can set you and your staffs computer up to make you reset your password after a specific time.
Ahhhh passwords! Seemingly the simplest way of protecting your secure information but somehow the one that so many fail on. Passwords should be strong, complex & memorable to only you. That means including numbers, punctuations, capital letters etc. They shouldn’t be obvious words like the same as your username, the word ‘password’ or your husband’s name (hackers have facebook too!) You should change your password at times too (eg every couple of months). We can set you and your staffs computer up to make you reset your password after a specific time. Updates/patches need to be done when a manufacturer finds a security issue that needs fixing. If you don’t carry out these updates, you’re leaving yourself wide open for security breaches. However, keeping on top of these updates is not easy. There are a lot of updates to cope with especially on a whole office worth of devices. This is where Patch Managment Software comes in. It deals with all the patches/updates for you from one device which can be someone at your office or here at Castle Computers. Contact us for more information on this effective and helpful software.
Updates/patches need to be done when a manufacturer finds a security issue that needs fixing. If you don’t carry out these updates, you’re leaving yourself wide open for security breaches. However, keeping on top of these updates is not easy. There are a lot of updates to cope with especially on a whole office worth of devices. This is where Patch Managment Software comes in. It deals with all the patches/updates for you from one device which can be someone at your office or here at Castle Computers. Contact us for more information on this effective and helpful software.